Key takeaways
• Ransomware complaints filed with the FBI rose 9% in 2024; the FBI describes ransomware as the most pervasive threat to critical infrastructure (FBI IC3 2024 Annual Report).
• The average ransom payment reached $2 million in 2024 — a fivefold increase from 2023 — while recovery costs averaged $2.73 million excluding any ransom paid (Sophos State of Ransomware 2024).
• Paying the ransom is not recommended: it does not guarantee data recovery, funds criminal activity, and increases the likelihood of repeat attacks.
• Reliable, isolated backups are the most effective recovery tool — but they must be protected from ransomware operators who routinely target backup systems.
• Effective ransomware protection requires multiple layers: behavioral threat detection, patched systems, MFA, email filtering, and user awareness training.
• Acronis Cyber Protect unifies backup and anti-ransomware detection in one platform, enabling automatic detection, termination, and file recovery without paying a ransom.
Ransomware is one of the most disruptive cyberthreats facing individuals and organizations today. Ransomware complaints filed with the FBI rose 9% in 2024 compared to the previous year, and the FBI has described ransomware as the most pervasive threat to critical infrastructure, according to the FBI’s 2024 Internet Crime Report. The good news: with the right defenses in place, ransomware is preventable — and recoverable.
What is ransomware?
Ransomware is malicious software designed to block access to your data until a ransom is paid. Once ransomware infects a device, it either encrypts your files or locks you out of your system entirely, then displays a ransom demand — usually requesting payment in cryptocurrency such as Bitcoin to obscure the transaction.
There are two main types of ransomware that individuals and organizations face:
Encryption ransomware
Encryption ransomware — the most common form — targets your files and documents. The malware scrambles your data using a cryptographic key, making files completely inaccessible. Your device continues to operate, but your documents, photos, and other files are locked until you pay for the decryption key. Cybercriminals increasingly pair encryption with data theft, threatening to publish stolen files publicly if the ransom is not paid — a tactic known as double extortion.
Locker ransomware
Locker ransomware locks you out of your device or operating system entirely rather than targeting individual files. The ransom demand typically appears as a full-screen message, preventing any normal use of the device until payment is made or the malware is removed.
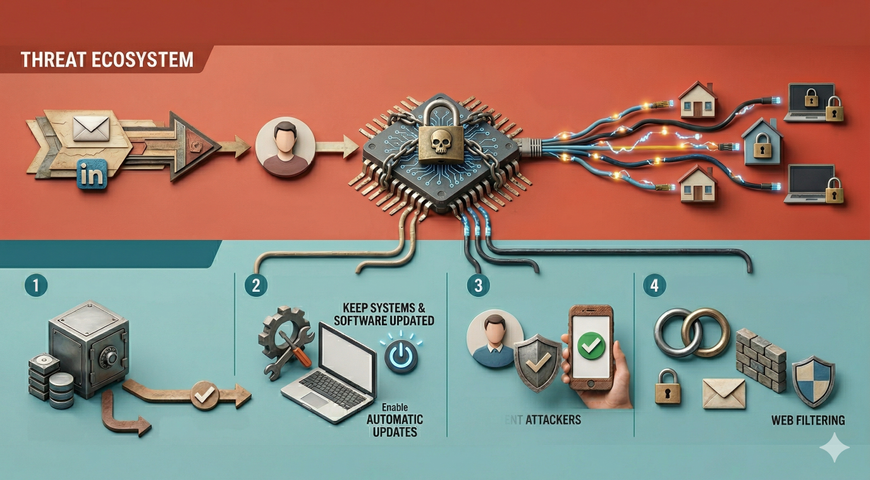
How does ransomware spread?
Ransomware reaches devices through several common vectors. Understanding these entry points is the first step to closing them off.
• Phishing emails: Ransomware is frequently delivered via malicious email attachments or links that trick recipients into executing the malware. A convincing email appearing to come from a trusted source can bypass even cautious users.
• Exploited vulnerabilities: Ransomware operators actively scan for unpatched software and operating system vulnerabilities. Systems that are not kept up to date are prime targets.
• Malicious downloads: Ransomware can be bundled into software downloads from untrusted sources or delivered via malicious websites that automatically execute code when visited.
• Remote desktop protocol (RDP) attacks: Cybercriminals exploit exposed or poorly secured remote access points to gain entry to systems and deploy ransomware manually.
• Cloud environments: Ransomware groups increasingly target cloud storage and services, encrypting data held in cloud repositories to maximize the impact of an attack.
Why ransomware remains a serious threat
Ransomware is not slowing down. According to the Sophos State of Ransomware 2024 report — based on a vendor-agnostic survey of 5,000 IT and cybersecurity leaders across 14 countries — 59% of organizations were hit by ransomware in the prior year. The average ransom payment reached $2 million, a fivefold increase from $400,000 in 2023. Recovery costs, excluding any ransom paid, averaged $2.73 million.
Even paying the ransom offers no guarantee. For the first time in 2024, more than half (56%) of organizations whose data was encrypted admitted to paying the ransom — yet many reported incomplete data recovery or faced repeat attacks. The FBI has explicitly advised organizations not to pay ransoms, as doing so funds criminal operations and does not ensure full restoration of systems.
Ransom demands have also escalated sharply. The Sophos report found that 63% of ransom demands in 2024 were for $1 million or more, and 30% exceeded $5 million — figures that extend to smaller organizations as well, with nearly half of businesses with revenue under $50 million receiving seven-figure demands.
How to protect yourself from ransomware
Preventing a ransomware attack is always preferable to recovering from one. The following measures significantly reduce your exposure and, critically, ensure you can recover without paying if an attack does succeed.
Back up your data — and test your restores
A reliable, regularly tested backup is the single most effective defense against ransomware. Ransomware operators cannot hold your data hostage if you can restore a clean copy from a secure backup. Follow the 3-2-1 backup rule: keep three copies of your data, on two different storage types, with one copy stored offsite or in the cloud.
Critically, backups must be isolated from your primary network. Ransomware groups routinely target backup systems to eliminate recovery options — the Sophos 2024 report found that ransomware operators attempted to compromise backup systems in the majority of attacks. Cloud backups with strong encryption and restricted access provide an additional layer of protection.
Keep systems and software updated
Unpatched vulnerabilities are one of the primary entry points ransomware operators exploit. Apply security patches promptly across operating systems, applications, and firmware. Enabling automatic updates where possible reduces the window of exposure between a vulnerability’s discovery and its remediation.
Use multi-layered security
No single security tool is sufficient. Effective ransomware protection combines behavioral threat detection, real-time monitoring, and endpoint security that can identify and halt ransomware activity — including from previously unknown ransomware variants. Behavioral analysis detects the patterns ransomware uses to encrypt files, rather than relying solely on known threat signatures.
Complement endpoint security with email filtering, web filtering to block access to malicious sites, and network monitoring to detect lateral movement by attackers who have already gained initial access.
Enable multi-factor authentication
Multi-factor authentication (MFA) adds a layer of verification that prevents attackers from using stolen credentials to access systems. Enable MFA across email, VPN, remote access tools, and administrative accounts — particularly backup management consoles, which ransomware operators target specifically.
Train users to recognize phishing
Because phishing is a leading delivery method for ransomware, security awareness training is a critical component of any defense strategy. Users should know how to identify suspicious emails, avoid clicking unknown links, and report unusual messages. However, training alone is not sufficient — technical controls must back it up, since even trained users can be deceived by sophisticated, targeted attacks.
Do not pay the ransom
Law enforcement agencies including the FBI strongly advise against paying ransoms. Payment does not guarantee data recovery, encourages further attacks against your organization, and funds criminal operations that victimize others. Organizations that pay are also more likely to be targeted again. Instead, focus resources on prevention, detection, and a tested recovery plan so that paying is never the only option.
How Acronis protects against ransomware
Acronis takes a unified approach to ransomware protection through Acronis Cyber Protect, which integrates backup, disaster recovery, and next-generation anti-malware in a single platform. Rather than relying on separate tools that cannot communicate with one another, Acronis combines detection and recovery so that both happen together.
At the core of this is Acronis Active Protection, a behavioral heuristics engine that continuously monitors system activity to detect and halt ransomware attacks in real time — including attacks from previously unseen ransomware variants. If ransomware begins encrypting files, Active Protection terminates the malicious process and automatically recovers any files that were affected, without data loss. Critically, Acronis also protects the backup software itself: its self-defense mechanism prevents ransomware from tampering with backup files or the backup agent, closing one of the most dangerous attack vectors that ransomware operators exploit.
For cloud backups, Acronis Cloud Storage uses end-to-end encryption and restricts file modification to authorized Acronis agent software only, ensuring that cloud-stored backups cannot be directly modified by malicious code.
This unified architecture means that even in a scenario where ransomware is not stopped before it begins encrypting data, recovery is fast, automatic, and complete — without ever having to consider paying a ransom.
Frequently asked questions
Can ransomware be removed without paying?
In many cases, yes. If you have a clean, isolated backup, you can restore your systems without paying the ransom. Law enforcement agencies including the FBI have also released decryption keys for several ransomware strains — since 2022, the FBI has provided decryption keys helping victims avoid over $800 million in payments. However, recovery without payment is far easier when a tested backup strategy is already in place.
Does antivirus software stop ransomware?
Traditional antivirus software that relies on known threat signatures can miss new and unknown ransomware variants. Modern anti-ransomware solutions use behavioral analysis to detect the patterns ransomware uses to encrypt files, regardless of whether the specific variant is known. Combining behavioral detection with secure backup provides the most comprehensive protection.
Should I pay the ransom?
The FBI, CISA, and cybersecurity experts consistently advise against paying. Payment does not guarantee your files will be returned in full, encourages future attacks, and contributes to the ransomware ecosystem. The better approach is to invest in prevention and recovery infrastructure so that paying is never your only option.
How does ransomware get onto my computer?
The most common entry points are phishing emails with malicious attachments or links, unpatched software vulnerabilities, malicious downloads from untrusted sources, exposed remote desktop connections, and compromised websites. Closing these entry points through patching, email filtering, and user training significantly reduces risk.
What makes Acronis Active Protection different from standard antivirus?
Standard antivirus typically detects threats based on known signatures and then alerts the user, but does not recover any data encrypted before the threat was detected. Acronis Active Protection uses behavioral heuristics to detect ransomware activity in real time — including unknown variants — terminates the malicious process, and automatically recovers any affected files from local caches or backups. Because it is built into the same platform as Acronis’s backup solution, detection and recovery work together rather than as separate tools.
About Acronis
A Swiss company founded in Singapore in 2003, Acronis has 15 offices worldwide and employees in 60+ countries. Acronis Cyber Platform is available in 26 languages in 150 countries and is used by over 21,000 service providers to protect over 750,000 businesses.